- November 1, 2022
- Cayley Wetzig, Head of Marketing Communications
The digital world is constantly evolving, and so are the hackers who inhabit it. As technology advances, so do the methods and tools used by those with malicious intent. Currently, about 30,000 websites are hacked each day.
To stay one step ahead of the game, it’s important to understand the hacker mindset. What motivates them? What makes their job easier? When you think like a hacker, you make it more difficult for these criminals to hurt your organization.
In this article, we’ll explore five specific things that hackers love. For each of these, we’ll provide a comprehensive solution to help you protect your business or organization. Let’s delve right in.
1. Vulnerabilities in Your System
Hackers love nothing more than finding vulnerabilities in your system. These weak spots can be exploited to gain access to sensitive data or wreak havoc on your network.
Here’s a look at some of the commonest system vulnerabilities:
Unpatched Software
Software applications are at the center of most organizations’ IT infrastructure. In fact, the average organization uses 254 SaaS applications and enterprises average 364 applications.
Unfortunately, software applications are also a major target for hackers. In 2019, 60% of all breaches were due to unpatched software.
It’s critical to keep all software applications up to date. This includes patching any security vulnerabilities as soon as they’re discovered.
Out-of-Date Software
As well as unpatched software, hackers also love taking advantage of out-of-date software. In particular, they’ll target applications that are no longer supported by the vendor.
This is because these applications are more likely to have known security vulnerabilities that haven’t been patched. Hackers can exploit these vulnerabilities to gain access to your system.
To protect your organization, you should always ensure that all software applications are kept up to date. This includes updating to the latest version when it’s released.
Poorly Configured Firewalls
A firewall is a critical component of any organization’s security strategy. It acts as a barrier between your internal network and the dangerous world of the internet.
However, a poorly configured firewall can actually do more harm than good. Hackers can use it to their advantage, gaining access to your network through open ports or vulnerabilities in the firewall itself.
To properly secure your network, make sure that your firewall is properly configured. This includes ensuring that all ports are closed unless they’re absolutely necessary.
Inadequate Anti-Virus Protection
Anti-virus software is another crucial element of any organization’s security strategy. It’s designed to detect and remove malicious software, such as viruses and Trojans.
Unfortunately, many organizations still don’t have adequate anti-virus protection in place. This leaves them vulnerable to attacks that can easily compromise their systems.
To properly secure your business, make sure that you have a robust anti-virus solution in place. This should be updated regularly to ensure that it can protect against the latest threats.
2. Lack of Security Awareness
The human factor is often the weakest link in any organization’s security. This is because employees can unwittingly expose the organization to risk. It’s no wonder that human error accounts for 95% of IT security breaches.
In what ways do hackers exploit the human factor?
Hackers love nothing more than finding vulnerabilities in your system. These weak spots can be exploited to gain access to sensitive data or wreak havoc on your network.
Here’s a look at some of the commonest system vulnerabilities:
Phishing Attacks
Phishing is a type of social engineering attack that involves tricking employees into disclosing sensitive information. Hackers will often send emails that appear to be from a legitimate organization. These emails will usually contain a link that leads to a malicious website.
Once an employee clicks on the link, they’ll be taken to a site that looks identical to the legitimate one. They’ll then be asked to enter their username and password. Once they do, the hackers will have access to their accounts.
These types of attacks are extremely common. In 2021, 83% of companies were targets of this type of cybercrime. That means if you haven’t been attacked yet, it’s only a matter of time.
To protect your organization, you should educate your employees about phishing attacks and how to spot them. You should also have a robust anti-spam solution in place to block these emails before they reach your employees.
Malicious Websites
Another way that hackers exploit the human factor is by creating malicious websites. These websites will often contain malware that can infect a computer if it’s accessed. The number of these websites is on the rise, with Google recording over 2 million phishing sites since 2020.
Hackers will usually use email or social media to spread links to these websites. They’ll often disguise the link as something innocuous, such as an interesting article or video.
Once an employee clicks on the link and visits the website, their computer will be infected with the malware. This can give hackers access to sensitive information, such as passwords and financial data.
Let your employees know about the dangers of clicking on links from unknown sources. You should also have a robust anti-malware solution in place to protect your systems.

Insecure Passwords
Poor password security now accounts for 81% of data breaches. This is because many people still use weak and easy-to-guess passwords.
Hackers love weak passwords as they’re easy to crack. Once they have access to one account, they can often use this to gain access to others. This is known as password reuse, and it’s a major security risk.
To protect your organization, you should always use strong and unique passwords. These should be at least eight characters long and contain a mix of letters, numbers, and symbols.
Invest in a reliable password manager to help you generate and store strong passwords. These tools can also help you avoid password reuse.
USB Drives
USB drives are another common way that hackers exploit the human factor. They’ll often leave these drives in public places, such as parking lots or coffee shops.
When an employee finds one of these drives, they’ll usually plug it into their computer to see what’s on it. Doing this will infect their computer with any malware that’s on the drive.
Warn your employees not to plug in any USB drives that they find. You should also have a policy in place for dealing with these types of devices.
Physical Security
Physical security is another area where the human factor can come into play. Hackers will often target employees who have access to sensitive areas, such as data centers or server rooms.
They’ll use social engineering techniques to trick these employees into letting them into these areas. Once they’re inside, they’ll be able to access sensitive information or plant malware on the network.
Make sure that you have strict physical security measures in place. Only allow authorized personnel to access sensitive areas. Use badge readers or other security devices to control access.
Insider Threats
An insider threat is an employee who deliberately or unintentionally exposes the organization to risk. This can be done through a variety of means, such as stealing data or careless social media posts.
Insider threats are a growing problem for organizations. An estimated 68% of companies now report feeling vulnerable to these threats.
There are a few things you can do to protect your organization from insider threats. First, educate your employees about the importance of security. Second, have a robust data classification system in place. And third, monitor employee activity for any red flags.
3. Unencrypted Data
When data is unencrypted, it can be easily accessed by anyone who has access to the network. This includes hackers, employees, and even third-party contractors.
Unencrypted data is a major security risk. Every day, a staggering 7 million data records that aren’t encrypted are compromised. The consequences of this can be disastrous for organizations, ranging from financial losses to reputational damage.
To protect your organization, you should encrypt all sensitive data. This includes data at rest, in transit, and in use. You should also have a comprehensive security policy in place that covers data encryption.
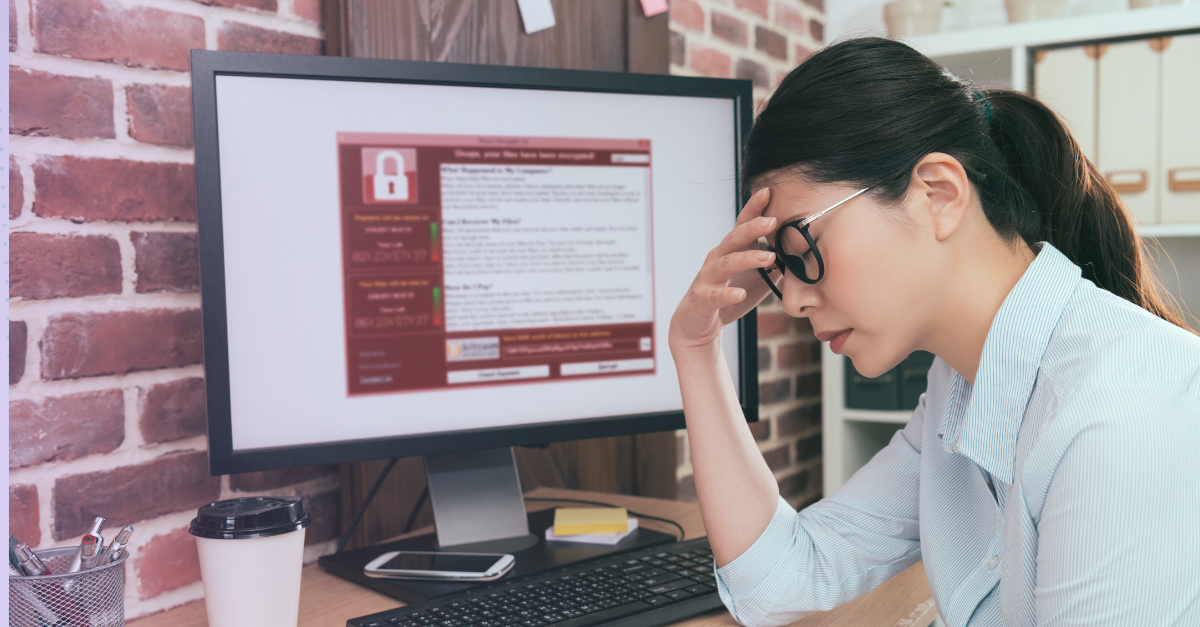
4. Data That's Not Backed Up
Incredibly, 96% of companies never back up the workstations they use. While hackers can’t always tell whether or not the data they’re targeting is backed up, it’s a huge bonus if they discover that it’s not. In the hacker mindset, unbacked-up data is a huge goldmine. If they’re looking for ransom, they can be sure that their demands will be met.
To protect your organization, you should have a robust backup and disaster recovery plan in place. This should include multiple backups stored in different locations. And it should be tested regularly to ensure that it works as expected.
5. Lack of Two-Factor Authentication
Two-factor authentication (2FA) is an extra layer of security that requires users to provide two pieces of evidence to prove their identity. This could be something they know, like a password, and something they have, like a code from a security key.
While 2FA isn’t bulletproof, it’s much more secure than using a single password. This is because even if a hacker manages to guess or steal your password, they still can’t access your account without the second factor. So effective is this security measure that it’s been reported to prevent 99.9% of all automated cyberattack
Keep Your Data Safe From Hackers
The threat of hacking is real and growing. The best way to keep your organization safe is to understand the hacker mindset. This means understanding the methods they use to gain access to systems and the types of data they’re after. By being a step ahead of them, you can make it much harder for them to succeed.
For more information on ThriveDX Security Awareness Training, please visit here.

Cayley Wetzig is ThriveDX’s Enterprise Divisions Head of Marketing Communications. She has worked at TigerGraph, IBM, Google, implemented Workday, started her own companies and has an MBA.
Protect Your Organization from Phishing
Explore More Resources
- Article, Blog
- Article, Blog
- Article, Blog
- Article, Blog
Your Trusted Source for Cyber Education
Sign up for ThriveDX's quarterly newsletter to receive information on the latest cybersecurity trends, expert takes, security news, and free resources.