Spoilers ahead! This post contains spoilers from Game of Thrones Season 8.
If you’ve been faithfully keeping up with Game of Thrones this season as we have, you’ll know it’s riddled with attacks, strategy, and information breaches. Just like the cyber world.
The Night King is defeated, but enemies still remain. These terrifying antagonists have much to teach us about how to approach cybersecurity.
Power in Numbers
What creates huge floods of traffic to overwhelm a target? If you guessed the Night King, you’re correct. If you thought botnets, you’re also right.

The Night King raised hordes of wights, zombie-like beings raised from the dead to do the White Walkers’ bidding. That’s why the Nights Watch burned the bodies of the dead – to prevent them from joining the Night King’s army. They’re brainless, but they act as pawns for the Night King. They’re bad news.
Botnets are eerily similar. They’re a network of infected devices under the control of the command-and-control servers (C&Cs). This army of connected devices can be used to carry out a distributed-denial of service (DDoS) attack, generate fake traffic, send spam, and other malicious activity. Most owners aren’t even aware their devices have been compromised – a terrifying thought.
The Night King might be gone, but in the real world, botnets are carrying out attacks that are steadily growing on average at a rate of 500%.
There’s no room for mistakes
Complacency can come with a huge cost. For seven seasons, all of Westeros feared Daenerys’ dragons. The dragons were a game changer for Daenerys. There’s no better defense than a fire breathing dragon, right?
Remember Season 7, when Bronn tried to take down the dragon Drogos with Qyburn’s scorpion. It didn’t work. But just like in the cyber world, attacks can become more sophisticated in nature. In The Last of the Starks, we see Euron Greyjoy and his fleet with bigger, stronger weapons. This ultimately cost Daenerys her dragon (RIP Rhaegal).
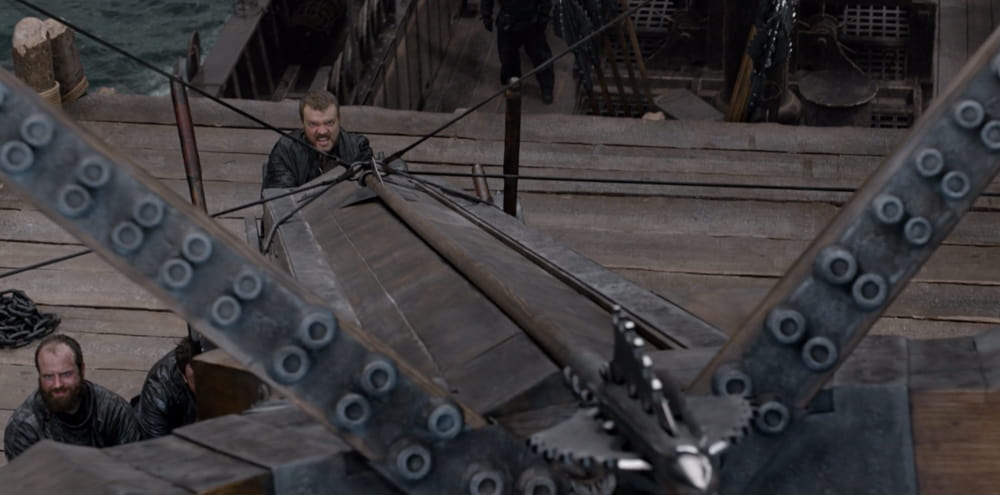
With an aerial view, Daenerys should have seen Euron and his fleet long before they had a good kill-shot. I believe she got complacent, feeling secure while flying a dragon.
The cyber moral here? Acquiring the strongest defenses is never a reason to get too comfortable. Attackers are constantly searching for ways to advance their methods. What is currently a strong defense can be outdated in the future. That’s why it’s particularly important to install those pesky software updates and patches. Staying a step ahead is key.
Its about the tools you have
Just as the wights in The Long Night were able to get past the, ahem, fire wall, hackers, too, can bypass your firewall.

That doesn’t mean firewalls aren’t a great tool to have in place. The key takeaway here is that a firewall won’t do you much good if you have other vulnerabilities. A good cybersecurity plan utilizes a variety of defenses.
Hit it at the source
Work smarter, not harder. In The Long Night, you’ll recall how grim the situation was. Loved ones were dying. Our protagonists were fighting for their lives, exhausted, getting repeatedly dogpiled by wights. Just when things couldn’t look any worse, the Night King raised all of their fallen comrades to join his army of the undead.
Luckily, the Night King wasn’t undefeatable. He had a weakness. Sure, he could raise thousands of more wights in mere seconds. But if he was defeated, all the wights would disappear, too.
If your device is infected with malicious software, you’ll have to fix the problem at its source, otherwise your efforts will be wasted.
A little preparation goes a long way
I consider Samwell Tarly the unsung hero of GoT. He might not be the best in combat, but he gave everyone a fighting chance against the Night King. Back in Season 3, he found that dragonglass can be used to kill the White Walkers. Without his research at the Citadel in Season 7, they wouldn’t have discovered the massive amount of dragonglass in Dragonstone and had it fashioned into weapons right before the big battle. That bit of preparation was the difference between staying alive or becoming one of the wights.
Thankfully, you don’t have to get your hands on any dragonglass to protect your cyber presence. Research and preparation can make a world of difference in staying ahead of attackers. That’s why we believe cyber skills education can go a long way.