Starting a new degree program or even modifying an existing program at your college or university is no easy task. However, with the rapidly changing technology and dependence on IoT, we are experiencing a surge in cybercrime and digital threats. At the same time, the world is suffering from a severe lack of qualified and skilled professionals in cybersecurity positions.
It is estimated that 3.5 million cyber security positions world-wide will be unfilled by 2021. With more students than ever attending college, why is this such an issue? And more importantly, how can we solve for it?
The cyber security industry is just now getting its well-deserved attention, and unfortunately, it’s long overdue. Some of the best companies in the world are having trouble filling above-average salary cybersecurity positions because there is no one to fill them. Going further back, there is no one to educate them.
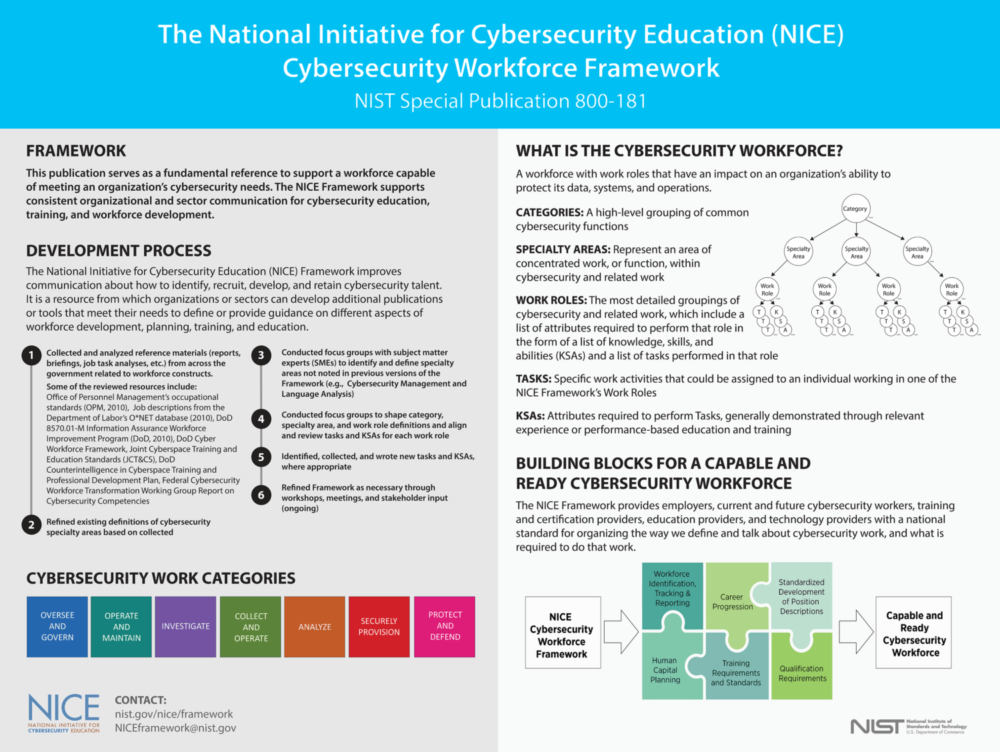
In the midst of this surfacing crisis, the United State Government has launched initiatives specifically for cyber security education that are designed to help schools (just like yours) develop the necessary degree programs. The National Initiative for Cybersecurity Education (NICE), led by the National Institute of Standards and Technology (NIST) in the U.S. Department of Commerce, is a partnership between government, academia, and the private sector focused on cybersecurity education, training, and workforce development.
Below is a description of each of the seven NICE Framework Workforce Categories which acts as a resource for curriculum development for your institution. To view the entire NICE Framework, click here.
- Securely Provision (SP): Conceptualizes, designs, procures, and/or builds secure information technology (IT) systems, with responsibility for aspects of system and/or network development.
- Operate and Maintain (OM): Provides the support, administration, and maintenance necessary to ensure effective and efficient information technology (IT) system performance and security.
- Oversee and Govern (OV): Provides leadership, management, direction, or development and advocacy so the organization may effectively conduct cybersecurity work.
- Protect and Defend (PR): Identifies, analyzes, and mitigates threats to internal information technology (IT) systems and/or networks.
- Analyze (AN): Performs highly-specialized review and evaluation of incoming cybersecurity information to determine its usefulness for intelligence.
- Collect and Operate (CO): Provides specialized denial and deception operations and collection of cybersecurity information that may be used to develop intelligence.
- Investigate (IN): Investigates cybersecurity events or crimes related to information technology (IT) systems, networks, and digital evidence.
In 2017, NICE established CAE National Resource Centers to provide an infrastructure for schools designated as Centers of Academic Excellence in Cybersecurity (CAE). CAE institutions receive formal recognition from the U.S. Government as well as opportunities for prestige and publicity for their role supporting our Nation’s information systems. If you think your school is ready to apply for CAE eligibility, visit: https://www.caecommunity.org/. If you’re unsure if your school meets the criteria, check out the application checklist for 2-year institutions here or for four-year colleges and graduate-level universities here.
Additionally, there are education solutions providers, such as Cybint Solutions, that complement existing curricula and adhere to the NICE and CAE guidelines. Our solutions were developed by military officials and cyber experts to provide the highest level of content to future cyber professionals. Learn more about Cybint’s educational solutions here: www.cybintsolutions.com/education.