A Cyber Security Analyst (CSA) or Incident Response Analyst is a professional that is trained to detect and prevent attacks to their organization or network. Protecting the security and integrity of data is vital for all businesses and organizations, and with cybercrime at an all-time high, it is no wonder why the demand for qualified Cyber Security Analysts (CSA) is surging. According to the U.S. Bureau of Labor Statistics (BLS), jobs in this field are projected to increase by nearly 30% between 2016 and 2026, which makes it one of the fastest-growing and in-demand occupations in the last decade.
Against that backdrop, an average annual wage as a Cyber Security Analyst sits at a competitive $99,815 as of October 2020. So, if you’re looking for a future-proof career, this may be the one for you. However, being a CSA is not for the faint of heart. In this article, Cybint covers what a day in the life of a CSA looks like – and it’s not what you expect!
Not Your Typical 9 to 5
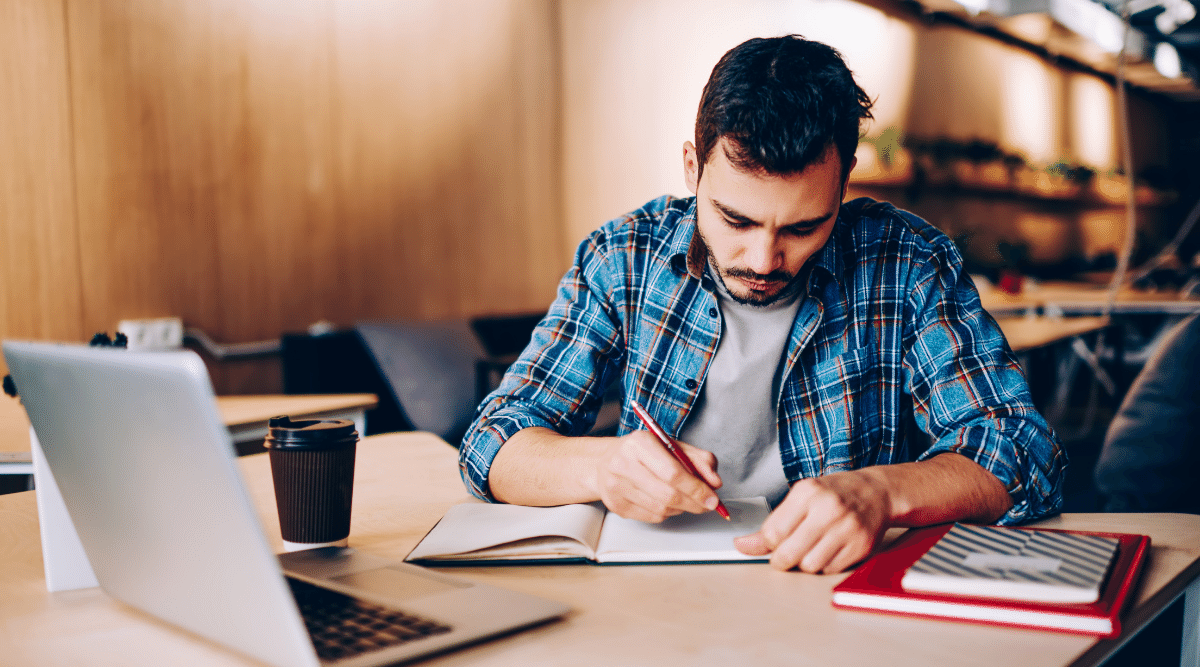
Regardless of the specific title of a cybersecurity professional, the day that lies ahead of them is unlikely to follow a generic 9 to 5 pattern. The unpredictable nature of information security means that though certain tasks will always need to be completed, such as checking in with the latest security news reports, the days’ events will likely differ from its predecessors. The likelihood is that Cyber Security Analyst face many exciting security challenges that ultimately require a lot of investigation, much like a police detective.
Know Your Vulnerabilities
For example, you are a CSA at a power plant that manages infrastructure on the East Coast. This plant provides electricity to millions of households and therefore, has a team of incident responders, such as yourself, working in their Security Operations Center (SOC). Someone in the company submits an IT request for a computer that keeps “re-setting” and is still connected to the company’s network.
Be Alert to Any and All Threats
Now, at this point in our example, the responsibility lies with IT, however, as an experienced CSA – it should pique your interest. In a company that is responsible for an incredible amount of infrastructure, your network is no doubt a target for determined hackers.
Communication is Key
As a CSA, throughout any investigations, you will work and communicate with many team members, not just IT and security. This is because many threats that do infiltrate the system, come through “regular” employees such as people in accounting, marketing, or HR. Those employees are not always on the lookout for threats and unfortunately in most cases are not properly educated on cybersecurity enough to prevent access or spear phishing to occur.
Consult Your Toolkit
However, in this example, you turn to IT first to investigate. After discussing with the IT shift manager, you both run several tests on the defective computer. First you test the anti-virus logs, and that’s not the issue. Then, you test system logs, the hardware, and Wireshark for network traffic analysis. Nevertheless, you find nothing conclusive.
Be Persistent
After running through multiple tests and attempts to find the culprit, you’re still out of luck. However, as a CSA, you cannot stop here, especially when there’s a chance that something much larger and more destructive is at play. Next, you dig deeper in the Network Access Control (NAC) and find alerts that were missed. After updating the SOC manager, you collect more information, unplug the defective computer from the network, and go back to the owner of the computer.
Ask A Lot Of Questions
The owner of the computer happens to be the company’s procurement director, so you decide to give her a call. You ask about anything out of the ordinary and discover that she received an unusual client email with a proposal attachment that was in a strange format. After investigating the suspicious attachment with IT, you come to the conclusion that the fake proposal was part of a social engineering attack on the company and the file was in fact, infected with malware.
Justice Is Served
You identified and intercepted an attempt to disrupt the power supply of the entire East Coast – you should be proud! You report the case to the FBI and assist with the investigation. Apparently, other power generators were attacked as part of the social engineering attack which led back to a group of known cybercriminals. Your work helped cease any damages and keep the power going for the community.
How’s that for a day’s work? If the high demand and impressive earning potential of a Cyber Security Analyst (CSA) is not enough to catch your attention, perhaps the exciting challenges and crime-fighting components did.
Cybint wants to work with you to get these skills and land the job. To see how we can empower your organization, learn more about our Cybint Bootcamp.
Together, we can put an end to cybercrime.